The privacy breach command center built for Canadian law.
BreachGuard is a privacy incident management platform that turns breaches into defensible, regulator-ready workflows — from the first report through RROSH assessment, commissioner notification, remediation, and a decade of immutable evidence. One platform, every Canadian framework — PIPEDA, PIPA, HIA, PHIPA, Law 25 and every provincial and territorial statute.
A spreadsheet is not an incident response plan. And it won't survive an OPC investigation.
Most Canadian organizations manage privacy breaches the same way: a shared tracker, an overflowing inbox, a hurried legal memo. It works — until the Privacy Commissioner asks for your records. Then every gap, every missed deadline, every undocumented judgment call becomes evidence against you.
BreachGuard replaces ad-hoc response with a defensible system of record that understands what each jurisdiction requires — and proves it happened.
Today
- Breach details tracked in a shared Excel file (if at all)
- Risk of Significant Harm assessed from memory, not method
- Commissioner notifications drafted from scratch each time
- SLA clocks tracked manually — or not tracked
- No immutable audit trail of who did what, when
- Multi-jurisdictional incidents double the work, halve the confidence
With BreachGuard
- Every incident captured in a structured, AI-assisted intake
- RROSH scored against configurable, weighted, defensible criteria
- Commissioner and individual notices AI-drafted, human-approved
- SLA countdowns automatically set from applicable frameworks
- Immutable audit log — 10-year retention by default
- Multi-framework mode applies the strictest rule automatically
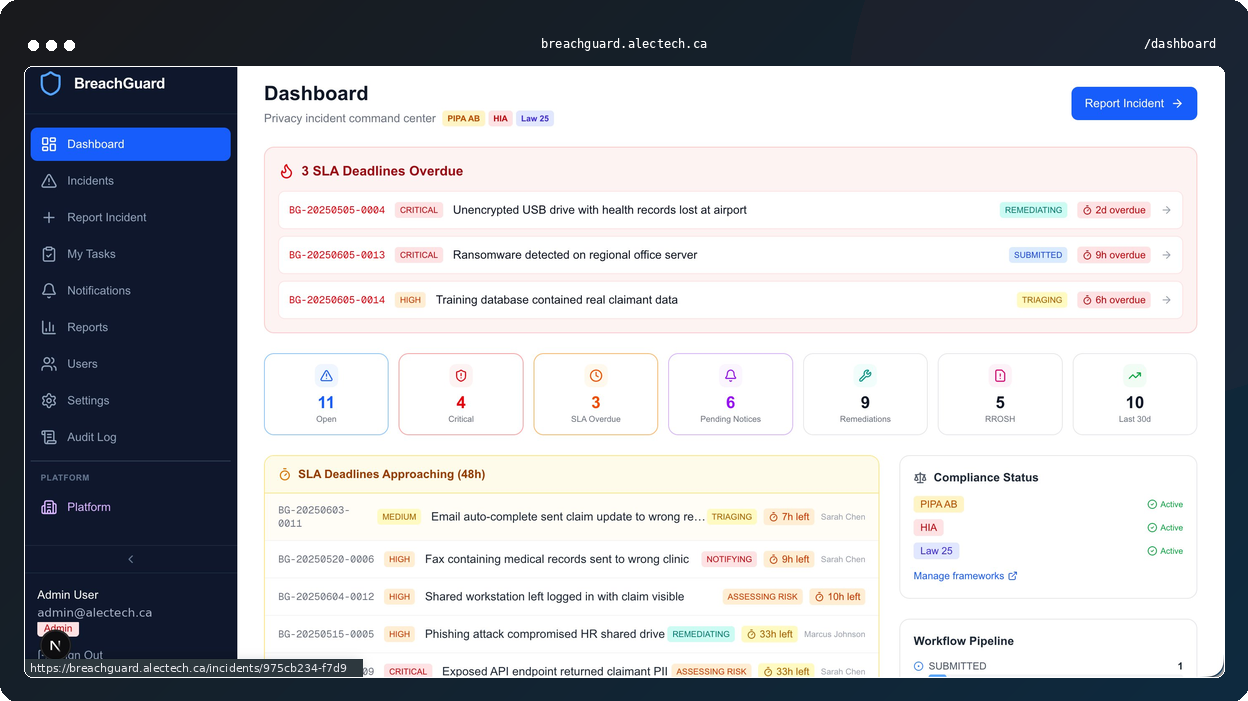
From discovery to closure, in one defensible workflow.
BreachGuard is organized around the six phases of Canadian privacy incident response — and the evidence obligations that attach to each one.
A structured front door for every incident.
BreachGuard's reporting form captures the data Canadian regulators actually require: incident category, types of personal information involved, affected population, containment status, and a narrative description. Anyone in the organization can file; the Privacy Office controls what happens next.
- AI-assisted categorizationLeave the category blank and BreachGuard suggests one from the description — with confidence score.
- Automatic data-type detectionThe model identifies SIN, health data, credentials, biometrics, and more from free-text.
- Role-based access from day oneReporters see only their own submissions; investigators and the Privacy Officer see the full record.
AI classification, human judgment, audit-ready record.
The moment an incident is submitted, BreachGuard proposes a category, priority, and summary. The Privacy Officer reviews, edits, or overrides — and every decision is logged. The SLA clock starts the second the incident is accepted, tied to the frameworks you've configured.
- Confidence-scored AI classificationSee why the model suggested a category, not just what.
- Deterministic SLA enforcementFramework-aware deadlines visible from the incident header.
- One-click PDF report exportRegulator-ready export of the incident record at any point in the workflow.
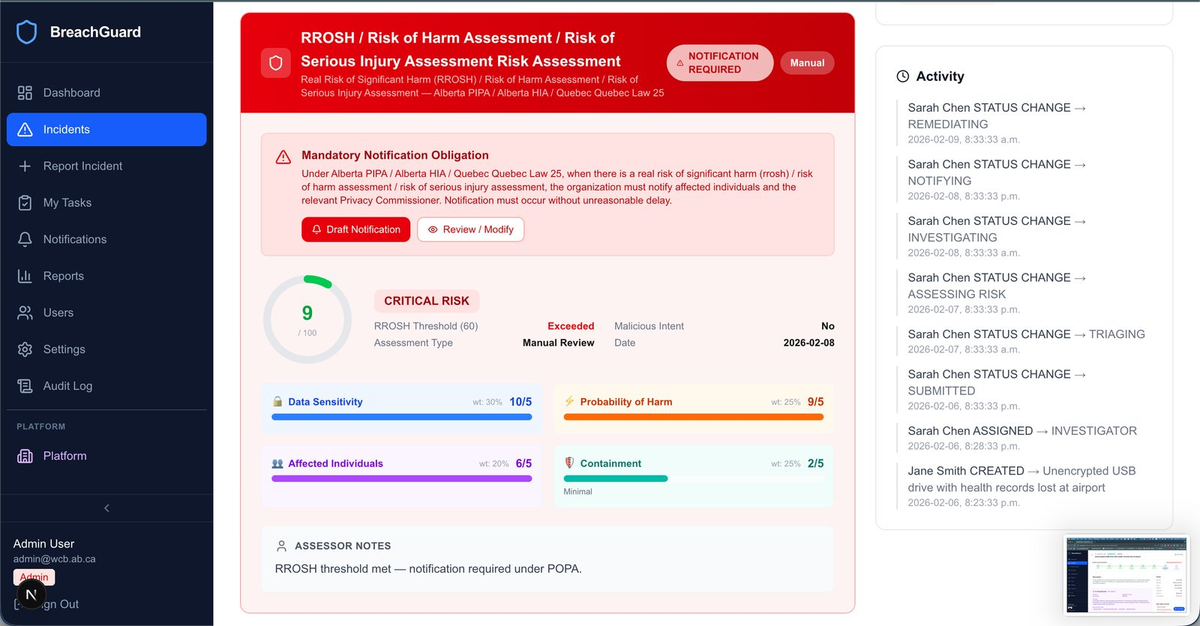
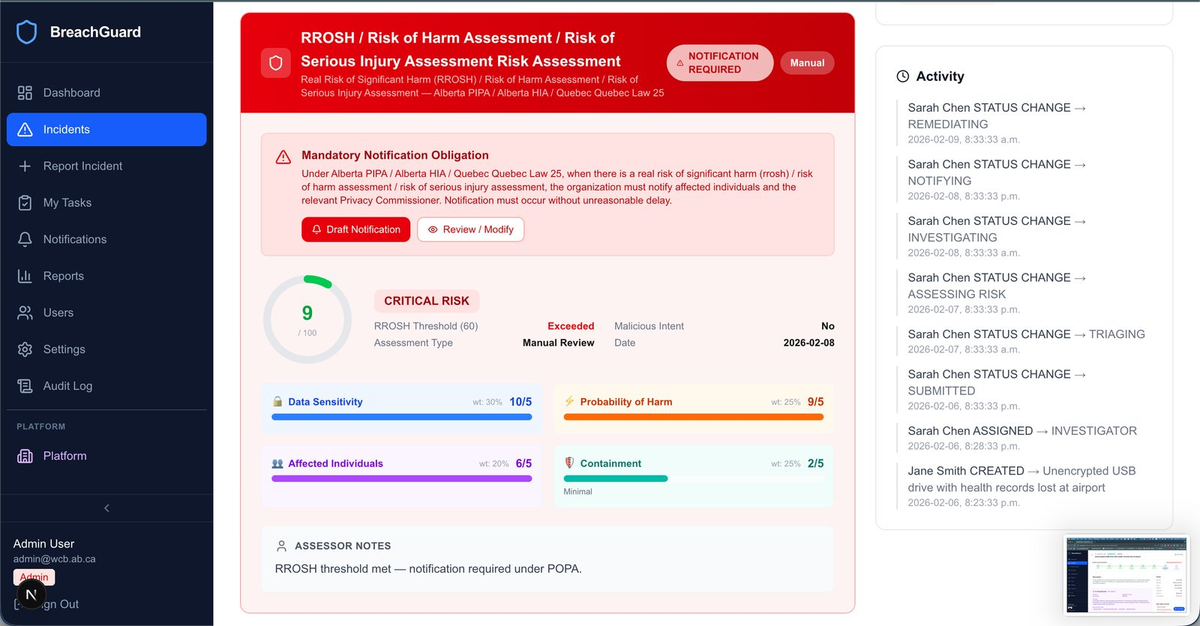
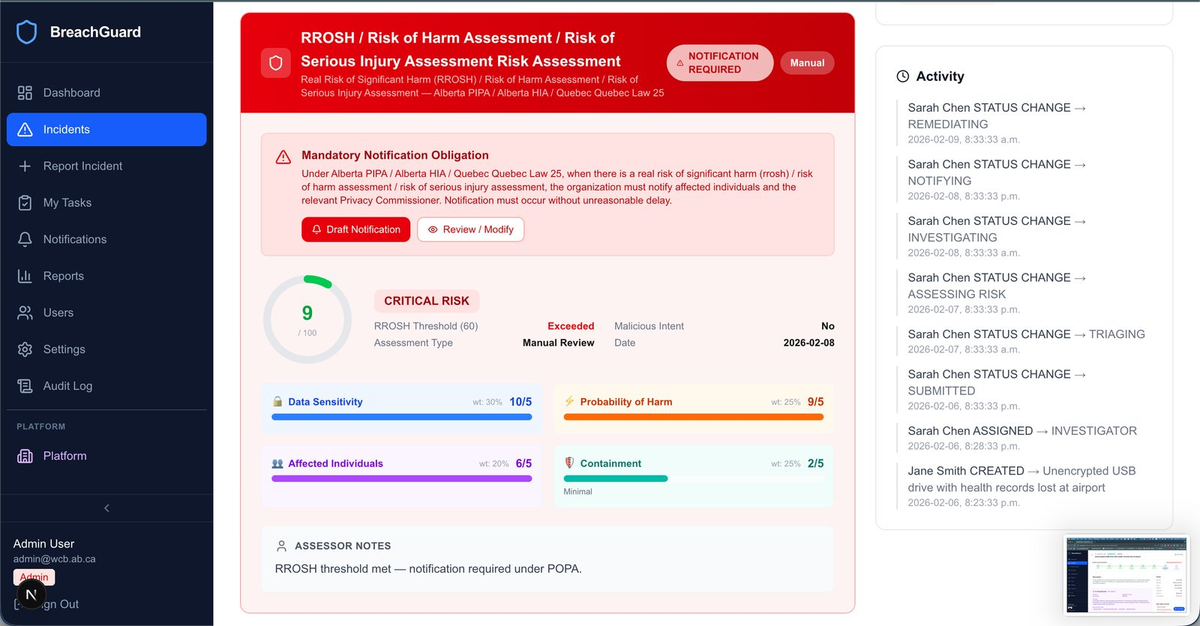
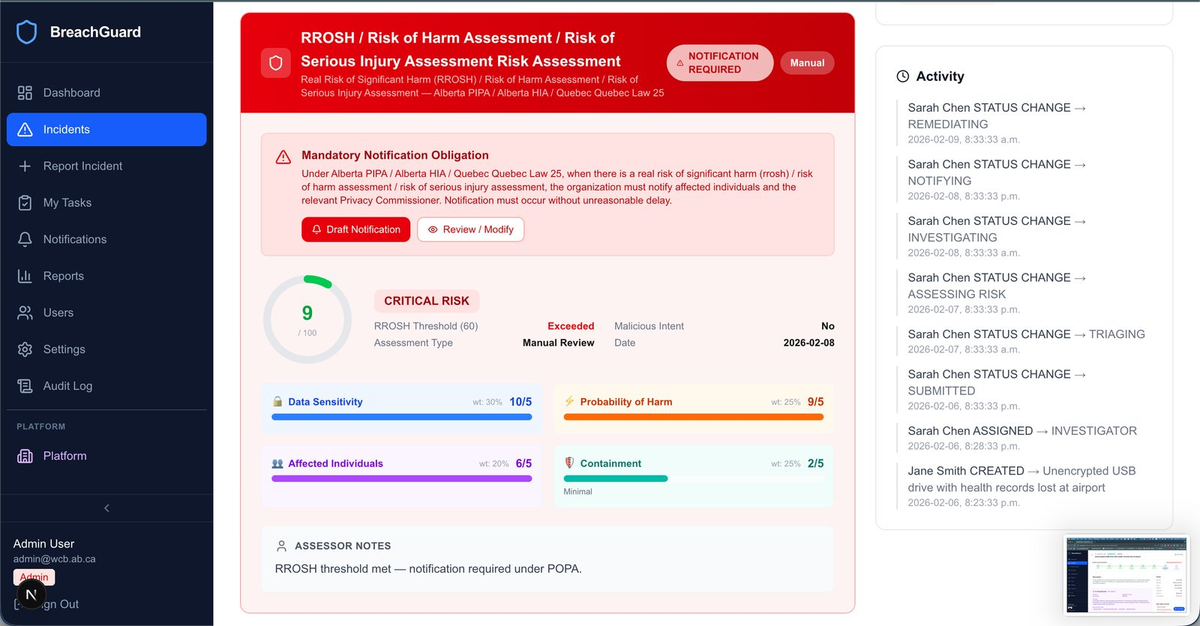
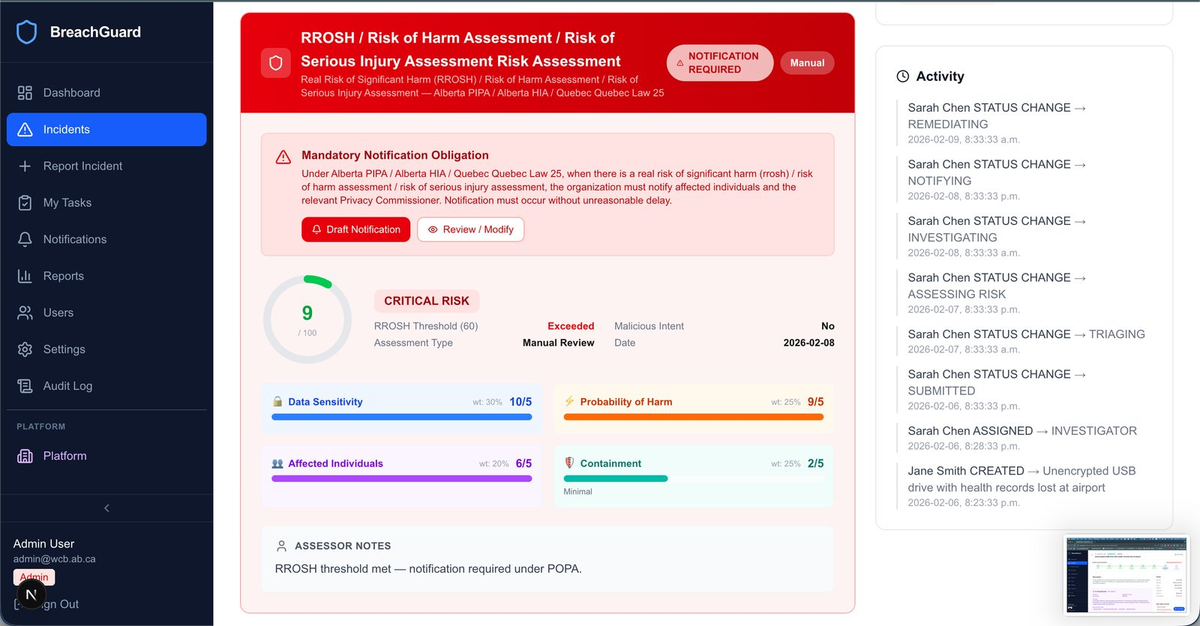
The Real Risk of Significant Harm, scored like evidence.
PIPEDA, PIPA Alberta, HIA and Québec Law 25 all turn on the same pivot: is there a real risk of significant harm? BreachGuard makes that judgment reproducible. Four weighted dimensions — data sensitivity, probability of harm, affected individuals, containment — roll up to a defensible score against a configurable threshold.
- Weighted, explainable scoringEvery factor is documented, every weight is configurable.
- Assessor notes fieldQualitative judgment captured alongside the quantitative score.
- Automatic notification gatingWhen the threshold is met, the notification workflow unlocks.
Commissioner and individual notices, drafted in minutes.
BreachGuard generates two notifications for every qualifying incident — one to the relevant Privacy Commissioner, one to affected individuals — pre-populated from the incident record and the applicable framework. The Privacy Officer reviews, edits, approves, and sends. The full lifecycle is tracked: Draft → Pending Review → Approved → Sent → Delivered → Acknowledged.
- Jurisdiction-aware templatesContent and addressing tuned to OPC, OIPC-BC, OIPC-AB, IPC-ON, CAI Québec.
- Separation of duties enforcedDrafter cannot self-approve. The workflow requires it.
- Delivery confirmation trackingKnow when the regulator opened it, and log it.
Corrective actions, tracked to completion.
Regulators don't close files because you notified — they close them because you fixed the underlying issue. BreachGuard turns lessons learned into tracked work: policy reviews, staff training, access control changes. Every task has an assignee, a due date, a priority, and a verifiable completion state.
- Kanban and list viewsPrivacy Officers run the board; individuals work their tasks.
- Overdue flaggingNothing slips through the cracks six months after the headline is gone.
- Linked to parent incidentRemediation evidence tied to the breach that prompted it — for life.
The board-ready view. Every framework, every quarter.
BreachGuard's Reports & Compliance module answers the question Privacy Officers get from leadership every quarter: are we meeting our obligations? Live compliance scorecards per framework, SLA attainment, RROSH-triggered notices, and record-retention posture — all exportable, all linkable to the underlying incidents.
- Per-framework scorecardsPIPEDA, PIPA, HIA, Law 25 each with their own obligations and metrics.
- Trend analyticsIncidents by month, by severity, by status, by business unit.
- Board & regulator exportsQuarterly package generation, no scrambling the week before the meeting.
An assistant that knows Canadian privacy law.
BreachGuard's AI isn't a chatbot bolted onto a form. It's framework-aware — ask it a question about a live incident and it responds in the context of the legislation you've configured. It knows HIA's five-day notification window. It knows Law 25's content requirements. It suggests. You decide.
Classification
Categorize incidents, detect personal-information types, suggest priorities — all with confidence scores you can see and override.
Drafting
Generate commissioner notices and affected-individual letters pre-populated from the incident record and applicable framework — then approve, edit, or reject.
Guidance
Ask: "given PIPA AB and HIA, what do we do next?" — and get a cited, framework-specific action list. Not opinion. Obligation.
The single most consequential judgment in Canadian privacy law.
Under PIPEDA, PIPA Alberta, HIA and Québec Law 25, one question decides whether you notify: is there a real risk of significant harm? Get it wrong, you underreport and face penalties. Get it wrong the other way, you overreport and erode trust. BreachGuard makes the judgment reproducible, weighted, and defensible.
Healthcare tenants can weight Data Sensitivity higher. Financial services can weight Probability of Harm higher. The model is configurable — and the configuration itself is audited.
See BreachGuard against your actual obligations.
A 30-minute working session with an AlecTech privacy engineer. We'll walk through a real incident end-to-end, configured for your jurisdictions. No slides. No marketing.
Every Canadian framework. Every obligation.
BreachGuard's multi-framework mode auto-configures SLAs, notification rules, and record-keeping requirements based on the legislation you operate under. When multiple frameworks apply, the strictest rule wins.
- Notify OPC and affected individuals of breaches creating real risk of significant harm
- Maintain breach records for 24 months minimum
- Safeguard personal information under your control
- RROSH scoring calibrated for PIPEDA weights
- OPC-templated notifications with delivery tracking
- 10-year immutable record retention
- Federal institutions must safeguard personal information
- Respond to privacy breaches per TBS guidance
- Maintain records of material breaches
- TBS-aligned incident workflow
- Material breach tracking and escalation
- Commissioner + individual notification pipeline
- Notify OIPC Alberta of RROSH-level breaches (s.34.1)
- Notify affected individuals without unreasonable delay
- Maintain records of breaches
- OIPC-AB templates pre-addressed
- Alberta jurisdiction tagging on notifications
- SLA countdowns visible from the dashboard
- Protect personal information against unauthorized access
- OIPC-BC notification strongly recommended
- Respond to privacy complaints and incidents
- BC jurisdiction routing for notifications
- Configurable gating at tenant level
- Full incident record retained regardless of notification
- Report confidentiality incidents to CAI with diligence
- Notify affected persons when serious harm risk exists
- Maintain a confidentiality incident register
- Penalties up to 4% of global revenue
- CAI French-language notification templates
- Confidentiality incident register as a first-class report
- Serious-risk threshold configurable apart from RROSH
- Notify OIPC Alberta of health information breaches
- Notify affected individuals and professional regulatory bodies
- Act at the earliest reasonable opportunity
- Auto HIA detection when health data is flagged
- Multi-party notification workflow
- AI assistant cites HIA timelines in guidance
- Health custodians must notify IPC Ontario
- Notify affected individuals at first reasonable opportunity
- Submit mandatory annual statistics to IPC
- IPC-ON templates and routing
- Annual statistics report generator
- Per-incident evidence pack export
- Health custodians must notify the NB Ombud
- Notify affected individuals of significant breaches
- Substantially similar to PIPEDA for health information
- NB Ombud notification routing
- Health-data auto-detection on intake
- PIPEDA-aligned RROSH treatment
- Trustees must take reasonable steps on breach
- Notify affected individuals where appropriate
- Notify the Manitoba Ombudsman when warranted
- MB Ombudsman templates
- Trustee-role RBAC
- Configurable notification threshold
- Trustees must notify affected individuals of significant breaches
- Notify the SK Information and Privacy Commissioner
- Take reasonable steps to remediate
- IPC-SK routing
- Significance threshold per organization
- Evidence vault for forensic attachments
- Notify the NS Review Officer of significant breaches
- Notify affected individuals without unreasonable delay
- Risk-of-significant-harm threshold applies
- NS Review Officer templates
- RROSH weights tuned for NS harm threshold
- Immutable audit trail
- Custodians must notify OIPC-NL of material breaches
- Notify affected individuals
- Deemed substantially similar to PIPEDA for health
- OIPC-NL routing
- Material-breach threshold configurable
- PIPEDA-aligned RROSH scoring
- Establish a Privacy Management Program (PMP deadline June 2026)
- Designate a Privacy Officer and classify personal information
- Mandate training; conduct PIAs on new programs
- PMP-ready program scaffolding
- Privacy Officer role + data classification system
- PIA workflow and training evidence tracking
- Public bodies must protect personal information
- Report breaches to IPC Ontario at first reasonable opportunity
- Municipal bodies covered under MFIPPA
- IPC-ON routing per body type
- Provincial / municipal toggle at tenant level
- Institution-head RBAC
- Public bodies must safeguard personal information
- Notify OIPC-BC and affected individuals of harmful disclosures
- Comply with BC-specific breach response standards
- OIPC-BC templates
- Harm threshold configurable per body
- SLA enforcement per BC public-body timelines
- Public bodies must safeguard personal information
- Respond to breaches per Manitoba Ombudsman guidance
- Maintain records of breach response
- MB Ombudsman templates
- Public-body classification tag
- Full audit trail
- Provincial and local-authority bodies must protect personal information
- Notify IPC Saskatchewan of significant breaches
- Notify affected individuals where warranted
- IPC-SK routing
- Provincial vs. local-authority mode
- Significance threshold per body type
- Public bodies must protect personal information
- Respond to breaches per NB Ombud guidance
- Notify affected individuals of significant harm
- NB Ombud templates
- Public-body classification
- Breach register aligned to RTIPPA record-keeping
- Public bodies must protect personal information
- NS Review Officer oversight applies
- Notify individuals of harm-causing breaches
- NS Review Officer templates
- Harm threshold configurable
- Immutable audit log
- Public bodies must safeguard personal information
- Respond to breaches with notification where required
- Maintain records aligned to PEI requirements
- PEI IPC templates
- Public-body workflow
- Retention aligned to PEI statutory floor
- Public bodies must protect personal information
- Notify OIPC-NL of breaches causing significant harm
- Notify affected individuals
- OIPC-NL routing
- Significant-harm threshold configurable
- Audit-log retention to NL statutory floor
- Territorial public bodies must safeguard personal information
- Respond to breaches per IPC Yukon oversight
- Notify affected individuals where required
- Yukon IPC templates
- Territorial jurisdiction tagging
- RBAC for smaller-body workflows
- Territorial public bodies must protect personal information
- Notify IPC NWT of material breaches
- Maintain records of breach response
- IPC-NWT routing
- Territorial classification
- Material-breach threshold configurable
- Territorial public bodies must safeguard personal information
- IPC Nunavut oversight applies
- Respond to breaches and notify where required
- IPC-Nunavut templates
- Territorial routing
- Audit log retention to statutory floor
BreachGuard is software, not legal counsel. This mapping reflects AlecTech's good-faith interpretation of current Canadian privacy law as of 2026 and is continuously updated as legislation evolves. Always consult qualified privacy counsel for applicability to your organization.
Three roles. One defensible record.
BreachGuard was designed with Privacy Officers, CISOs, and legal counsel in the room. Each role gets what they need — and only what they need.
Run your program from a single pane.
- Real-time SLA and workflow dashboards
- Approval queues for notifications and remediation
- Multi-framework posture tracking, per-jurisdiction
- Board-ready quarterly reporting, one click
Bridge security events to privacy obligations.
- API and SIEM integration for automated incident creation
- Data-type detection that aligns with DLP classifications
- Role separation that satisfies SOC 2 and ISO 27001 reviewers
- Evidence vault for forensic attachments
Build the record you'll need in discovery.
- Immutable audit log with actor and timestamp on every event
- Per-incident PDF export suitable for regulator or court
- Mapping from every action to the legal obligation it discharges
- Configurable retention aligned to provincial requirements
Answered plainly.
Where is BreachGuard data hosted?
All customer data is hosted in Canadian data centres. BreachGuard is operated by AlecTech Inc., a Canadian-incorporated, Canadian-owned company headquartered in Mississauga, Ontario. Data does not leave Canadian jurisdiction under our standard deployment.
For enterprise customers with more stringent requirements — for example, sovereign cloud or air-gapped deployment — we offer dedicated tenant architectures on request.
How long does onboarding take?
A standard BreachGuard tenant can be stood up in 3–5 business days: framework selection, user provisioning, notification template customization, and a guided walk-through with the Privacy Officer. Add 1–2 weeks if you'd like to pair it with our Data Inventory Kickstart engagement.
Does BreachGuard integrate with our SIEM or ticketing system?
Yes. BreachGuard exposes a REST API for incident creation and status updates, webhook emission for state transitions, and prebuilt connectors for common SIEMs (including our sister product Themis) and ticketing systems. ServiceNow, Jira Service Management, and Microsoft Sentinel integrations are supported out of the box.
Is this AI going to hallucinate a notification and get us sued?
The AI drafts; humans approve. Every AI-generated output in BreachGuard — classifications, notifications, remediation suggestions — is labelled as a suggestion, scored for confidence, and requires explicit human approval before any external action is taken. Nothing is sent to a regulator or an affected individual without a named human signing off, and that approval is captured in the audit log.
That said, you can disable AI features entirely at the tenant level. Some customers prefer a fully manual workflow, and BreachGuard supports that too.
How is BreachGuard priced?
BreachGuard is licensed per-tenant with tiers based on user seats, number of legal entities covered, and integration footprint. Pricing includes unlimited incidents, all jurisdictions, and the AI features. We are happy to share a quote tailored to your organization during the discovery call.
What frameworks will BreachGuard support next?
Our roadmap prioritizes Canadian coverage first — all 24 federal, provincial, and territorial privacy statutes are already in scope. We are actively scoping support for CPPA (when proclaimed in force) and select US state laws driven by customer demand. We do not currently support GDPR or CCPA natively; customers with European or California obligations typically pair BreachGuard with a dedicated regional platform.
Can we export our data if we leave?
Yes. All incident records, notifications, audit logs, and remediation histories are exportable in structured formats (JSON and CSV) and as PDF packages per incident. Your data is your data — we don't hold it hostage, and we never will.
See BreachGuard against your actual obligations.
A 30-minute working session with an AlecTech privacy engineer. We'll walk through a real incident end-to-end, configured for your jurisdictions. No slides. No marketing.

